by Eliézer Pereira
1 Goal
The purpose of this article is show how to perform a RAM memory forensic analysis, presenting some examples of information that can be retrieved and analyzed to help identify indications of security incidents as well as fraud and other illegal practices through information systems.
2 Good Practices and Techniques for Computer Forensic Analysis
2.1 NIST 800-86
The National Institute of Standards and Technology (NIST) is known worldwide for the publication of documents that bring well detailed and well comprehensive technology standards.
Document 800-86 – Guide to Integrating Forensic Techniques into Incident Response has a number of recommendations for proceeding with forensic analysis of security incidents, from data collection to the preparation of a final report.
2.1.1 Steps for Forensic Analysis, according to NIST
Collect – Identify, label, and proceed with the acquisition of data from diverse sources, in a documented way and ensuring the integrity of the data.
Examine – Process the collected data, which usually requires manual methods and automated forms, already trying to identify possible data relevant to the investigation.
Analyze – Continue processing in a more careful way and already having a direction to investigate. At this stage too collections of other data sources can bring additional evidence.
Report – Describe the result of the analysis that must include the report of everything that has been done since the first stage. Report actions taken, as well as tools and procedures used. Analyze other risks and suggest improvements for internal controls and tools, in order to reduce the impact to the business by detecting weaknesses that can cause recurrence of an incident, for example.
2.2 RFC 3227
RFC 3227 provides good practice for acquiring digital evidence. The order in which data are collected can determine the success or failure of an investigation.
This order is called the Volatility Order, which as its name suggests, directs that volatile data must be collected first. Volatile data is any data that can be lost with system shutdown, such as a connection to a website that is still registered with RAM. We must prioritize the acquisition of evidence from the most volatile to the least volatile:
* Caches
* Routing tables, process tables, memory
* Temporary system files
* Hard drive
* Remote logs, monitoring data
* Physical network configuration, network topology
* Media files (CDs, DVDs)
3 RAM Memory Analysis
The Random Access Memory (usually abbreviated to RAM) is a type of memory that allows reading and writing, used in digital electronics. When running a program, it is read into a storage device. A CD, for example, is transferred to the RAM, and then it will be run by the processor. Access to RAM is advantageous because it has much higher transfer rates than the hard disk.
The disadvantage is the loss of data stored when the computer is turned off. When the computer is turned on, the boot process of the boot system is redone having libraries, drivers and preference settings copied back to the RAM. The RAM memory can contain several types of files from executable programs and network communication port information to operating system log files, web browsing logs, photos, text files, etc.
As previously mentioned, this content can be lost when the machine shuts down, and in computer forensic analysis, the aforementioned Volatility Order must be followed mandatorily, to ensure that evidence is not lost.
3.1 Creating a RAM Memory Image
The software used for this purpose will be the “DumpIT” free software found here.
Recommendation:
The image should not be written directly to the machine that will have the analyzed RAM. The software “DumpIT” must be copied and run from an external storage device (for example a flash drive, external HD or even a secure network share).
Execution:
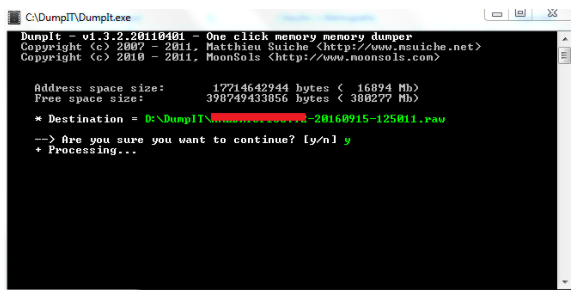
Run the “DumpIT” software with administrator privileges:
The Software “DumpIT” will display as below, the memory size “Address space size”, which in the example displays a 16GB of RAM, where the result of the image file generated will have approximately the same size. The path where the file is saved is shown in “Destination” and is the path where the program “DumpIT” is running.
By default the file name is the hostname (hostname) followed by the date of execution of the imaging process. The file is saved by default in “raw” format.
To start the process, simply press the “Y” key.
The “Processing” message indicates that the forensic image memory is being processed.
The “Success” message indicates that the process was successfully completed:
4 Volatility Framework
To show some basic examples of evidence that can be found in RAM, we will need to analyze the generated files. For this purpose we will use the Volatility Framework software.
The Volatility Framework is a collection of free and open source tools for RAM analysis. It is usually used in Linux environments, and already present in some distributions, such as Kali Linux for example.
We will use Volatility in a Windows environment, having no impact on the result or the commands used.
Download: http://www.volatilityfoundation.org/25
4.1 Plug-ins
Plug-ins are modules that will perform a specific function in generated image files. As the focus is only to demonstrate some plug-ins, I suggest you read about the others (and there are many others!) at the link mentioned above.
4.2 Extracting Information
Imageinfo – displays operating system information
This plug-in will bring the essential information for analysis as it will identify the profile that will be used by all other plug-ins.
Command Used:
Volatility -f 20160915-125011.raw imageinfo
In the “Suggested Profile” line, always use the first suggestion. Here we can see that the operating system is Win7SP0x86 (Windows 7, with no service pack installed, the 32-bit version). From the information of the profile, we can now use other plug-ins.
Pslist – List Processes Running:
Command:
Volatility -f 20160915-125011.raw -profile = Win7SP0x86 pslist> pslist.txt
-f “filename”
“-profile = Win7SP0x86” – Directs to use the operating system profile previously detected.
pslist – Plug-in to run
> pslist.txt – Instruction to create a text file with the same name as the plug-in, which allows a better view, and record the output for later analysis.
We can see all the processes that were running at the moment of the forensic image, including the software used for this.
Dlllist – Displays list of loaded dlls for each process
Command:
Volatility -f 20160915-125011.raw -profile = Win7SP0x86 dlllist> dlllist.txt
-f “file name”
“-profile = Win7SP0x86” – Directs to use the operating system profile previously detected.
DllList – Plug-in to run
> dlllist.txt – Instruction to create a text file with the same name as the plug-in
This command generate a large file, listing the executables and their DLLs in a very detailed manner, including the path of each of these DLLs. It would be useful, for example, to identify malicious files being loaded along with programs already known to the operating system.
Netscan – Displays network connections
Command:
Volatility -f 20160915-125011.raw -profile = Win7SP0x86 netsca> netscan.txt
-f “file name”
“- Profile = Win7SP0x86” – Directs to use the operating system profile previously detected.
netscan – Plug-in to run
> netscan.txt – Instruction to create a text file with the same name as the plug-in.
This is perhaps one of the most useful plug-ins used by Volatility. It brings very important information as well as protocols, ports, IPs, and executables involved in the network communication of the machine in question. With this information we could identify possible connections to suspicious IP addresses, for example.
Dumpregistry – Extracts log files
Command:
Volatility -f 20160915-125011.raw -profile = Win7SP0x86 dumpregistry -dump c: \ registry-dump
-f “file name”
“- Profile = Win7SP0x86” – Directs to use the operating system profile previously detected.
dumpregistry –dump – Plug-in to run + path of the directory where the log files will be extracted.
Several Windows registry files will be extracted from the image, but we will work with the four main ones, described below.
The “SYSTEM, SOFTWARE, SAM, NTUSER” log files contain a lot of information regarding operating system installation information, installed software, credential information, user-level information such as latest open files, network information, etc.
Change the name of the files to this default below:
- SYSTEM.REG
- SOFTWARE.REG
- SAM.REG
- NTUSER.DAT
4.3 Analyzing Log Files
We can use the software Registry Report to create a general report with all the information found in registry files.
Download: http://www.gaijin.at/dlregreport.php
Click on “File”, “Open registry files” and select “Import from folder”, locate the previously extracted files and click “OK”.
Then again in “file” select “Create Report”
Save the report.
The generated report will already bring information from chosen registry files:
5 Conclusion
The idea was show in a simple way, how important evidence can be extracted through the Memory RAM analysis.
Good practices for evidence acquisition have shown that steps should be followed systematically, because a wrongly executed procedure can lead to the loss of important evidence to solve an investigation.
6 References
Melo, Sandro. Computer Forensics and Free Software, High Books, 2009. ISBN, 8576082888, 9788576082880.
Morimoto, Carlos Eduardo. Hardware II, the definitive guide – Porto Alegre: Southern Editores, 2010. 1086 p. ISBN 978-85-99593-16-5. 1.
NIST SP 800-86 – Guide to Integrating Forensic Techniques into Incident Response http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-86.pdf
RFC 3227 – Guidelines for Evidence Collection and Archiving http://www.rfc-base.org/rfc-3227.html
About the Author
Eliézer Pereira is an IT and Security Professional with +10 years of experience. He is a graduate in Computer Networks, with an MBA in Information Security Management and certifications such as ITIL, ISO27002, Ethical Hacking, and AccessData Examiner. His work at the moment is focused on forensic investigations and security incident response.






















Great article – BlackLight makes it a whole lot easier: https://www.blackbagtech.com/blog/2017/02/22/windows-ram-part-triage/